Securing the Windows Secure Channel (Schannel) Library
While there have been many threats in SSL/TLS encryption in the past two years, new standards and security principles have also been established. Unlike Linux, which uses the OpenSSL library, Windows uses the Windows Secure Channel (Schannel) Library for SSL/TLS encryption. While this protected you from the so-called heartbleed bug, other bugs (such as Poodle) were later found in the outdated encryption standard SSL (the predecessor of the current TLS standard). Windows server system administrators should pay attention to these.
Unfortunately, the default settings of Schannel for Windows server versions 2008 R2 – 2012 R2 aren’t ideal and are no longer state-of-the-art. For instance, SSL versions 2.0/3.0, dating back to 1995/1996, are still active by default on server 2008 R2. Both encryption standards are now considered security risks and should be replaced by TLS 1.0 – 1.2 as quickly as possible. The same goes for stream cipher RC4 (BEAST).
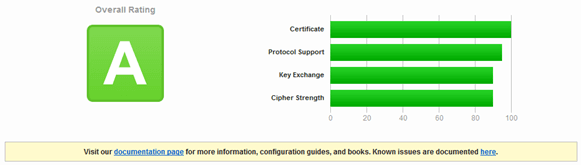
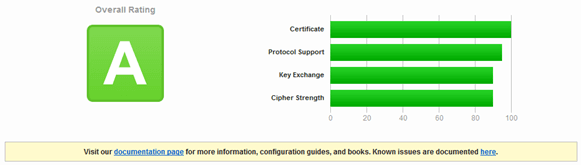
The status of SSL/TLS published HTTPS websites can be checked via IT security company Qualys’ SSLTest. If the test yields results similar to the one below, the Schannel library should be configured as described in order to get an A rating.
Step by step: how to improve Windows server 2008 R2 with Schannel configuration
The test result for the Windows server 2008 R2 without updates and default setting looks like this:

The current version 2012 R2 looks better:

However, even server 2008 R2 can yield an A rating if you take the following steps. The Schannel configuration functions exclusively via the registration key below HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL and SOFTWARE\Policies\Microsoft\Cryptography\Configuration\SSL in the Windows registry (please note that changes will only become active after a restart).
Steps to improve Windows server 2008 R2 with Schannel configuration
- Installation of all available Windows security patches
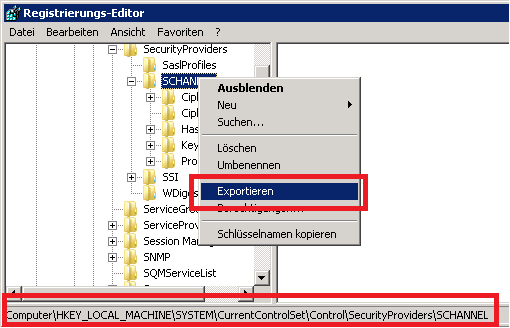
- Back up Registry Key Schannel (storage location of Schannel configuration)
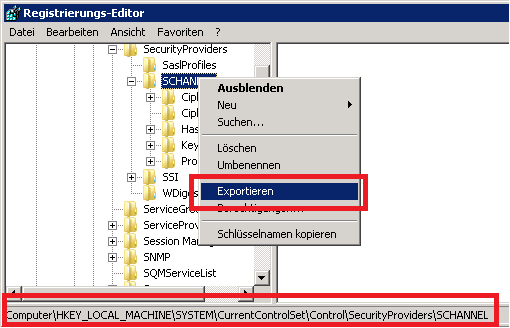
- Back up Registry Key SSL (storage location of cipher suite order)
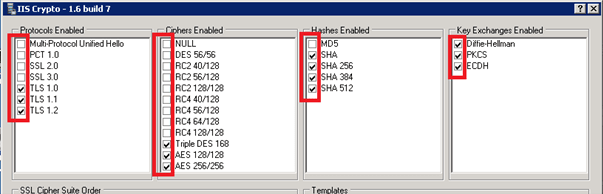
- The precise documentation of registry settings for Schannel can be found in the Microsoft KB article KB187498 and on the TechnetBlog. Alternatively, you can manage settings via the IIS Crypto tool:
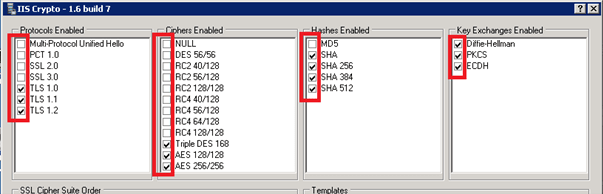
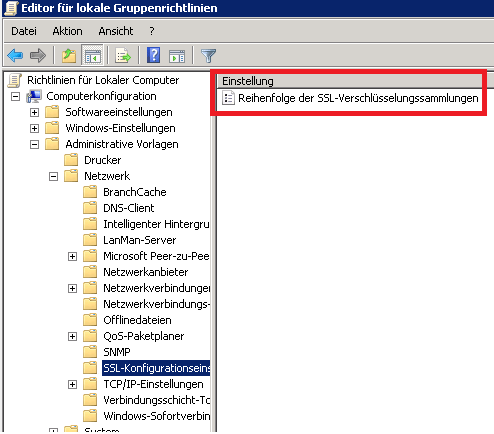
- Subsequently, the preferred cipher suite order needs to be modified to activate the security feature Perfect Forward Secrecy.
Rearranging can happen via a suitable group policy in Computer Configuration > Administrative Templates > Network > SSL Configuration Settings > SSL Cipher Suite Order.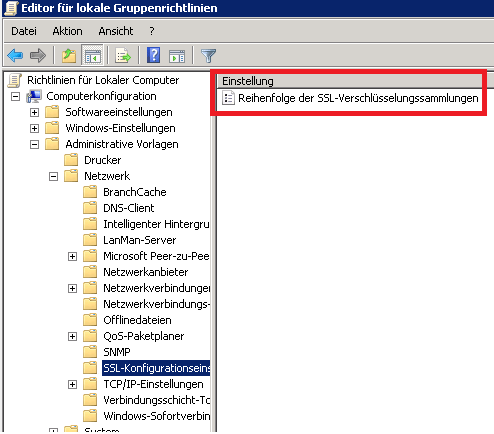
Alternatively, you could use the IIS Crypto tool to achieve this. This is a recommended order:
‘TLS_ECDHE_ECDSA_WITH_AES_256_GCM_SHA384_P521’,
‘TLS_ECDHE_ECDSA_WITH_AES_256_GCM_SHA384_P384’,
‘TLS_ECDHE_ECDSA_WITH_AES_128_GCM_SHA256_P521’,
‘TLS_ECDHE_ECDSA_WITH_AES_128_GCM_SHA256_P384’,
‘TLS_ECDHE_ECDSA_WITH_AES_128_GCM_SHA256_P256’,
‘TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA384_P521’,
‘TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA384_P384’,
‘TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA384_P256’,
‘TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA_P521’,
‘TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA_P384’,
‘TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA_P256’,
‘TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA256_P521’,
‘TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA_P521’,
‘TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA256_P384’,
‘TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA256_P256’,
‘TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA_P384’,
‘TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA_P256’,
‘TLS_ECDHE_ECDSA_WITH_AES_256_CBC_SHA384_P521’,
‘TLS_ECDHE_ECDSA_WITH_AES_256_CBC_SHA384_P384’,
‘TLS_ECDHE_ECDSA_WITH_AES_256_CBC_SHA_P521’,
‘TLS_ECDHE_ECDSA_WITH_AES_256_CBC_SHA_P384’,
‘TLS_ECDHE_ECDSA_WITH_AES_256_CBC_SHA_P256’,
‘TLS_ECDHE_ECDSA_WITH_AES_128_CBC_SHA256_P521’,
‘TLS_ECDHE_ECDSA_WITH_AES_128_CBC_SHA256_P384’,
‘TLS_ECDHE_ECDSA_WITH_AES_128_CBC_SHA256_P256’,
‘TLS_ECDHE_ECDSA_WITH_AES_128_CBC_SHA_P521’,
‘TLS_ECDHE_ECDSA_WITH_AES_128_CBC_SHA_P384’,
‘TLS_ECDHE_ECDSA_WITH_AES_128_CBC_SHA_P256’,
‘TLS_RSA_WITH_AES_256_GCM_SHA384’,
‘TLS_RSA_WITH_AES_128_GCM_SHA256’,
‘TLS_RSA_WITH_AES_256_CBC_SHA256’,
‘TLS_RSA_WITH_AES_256_CBC_SHA’,
‘TLS_RSA_WITH_AES_128_CBC_SHA256’,
‘TLS_RSA_WITH_AES_128_CBC_SHA’
‘TLS_RSA_WITH_AES_256_GCM_SHA384’ and ‘TLS_RSA_WITH_AES_128_GCM_SHA256’ should only be active on server 2012 R2 since the relevant update KB2992611 for earlier server versions includes errors that can lead to connection termination (see KB article).
Windows Server 2016 includes new cipher suites based on GCM. Additionally, the key length has increased to 2048 Bit (Logjam). Thus, for server 2016 the following orders may be put at the very beginning (in addition to the previous order):
‘TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384_P521’,
‘TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384_P384’,
‘TLS_ECDHE_RSA_WITH_AES_128_GCM_SHA256_P521’,
‘TLS_ECDHE_RSA_WITH_AES_128_GCM_SHA256_P384’,
‘TLS_ECDHE_RSA_WITH_AES_128_GCM_SHA256_P256’,
‘TLS_DHE_RSA_WITH_AES_256_GCM_SHA384’,
‘TLS_DHE_RSA_WITH_AES_128_GCM_SHA256’,
Please note that Cipher TLS_ECDHE_ECDSA_* are only active for ECC certificates (Eliptic Curve Cryptography) and not for normal certificates based on a RSA Private Key.
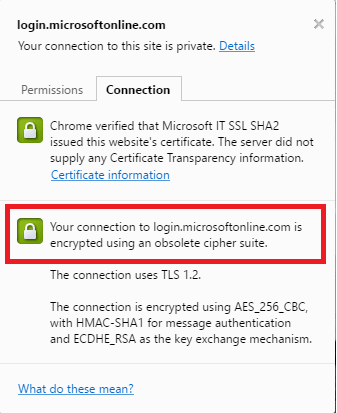
Google’s Chrome browser currently displays the notification ‘obsolete cipher suite’ in the connection properties for all cipher suites that aren’t based on GCM and Perfect Forward Secrecy.
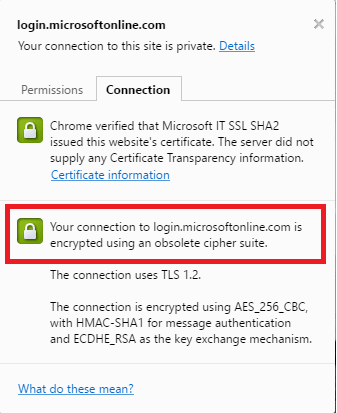
This warning with Schannel can currently only be avoided with an ECC Certificate (using the ECDSA Cipher with GCM) or the future use of Windows Server 2016.
- The modified configuration is only active after a server restart and should trigger an A rating for the SSL test:
Secure Channel, also known as Schannel, is the library Windows uses for SSL and TLS encryption.
TLS is the current encryption standard, while OpenSSL is its predecessor.
Because the SSL encryption standard is considered to be outdated, TLS is the better option.